Fritz
Adept
    
Gender: 
Posts: 1746
Reputation: 7.61
Rate Fritz

  
|
 |
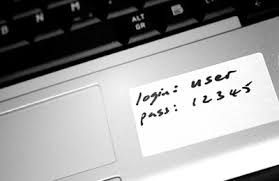
The LOT OF YOU might as well pick 'em from Scrabble dictionary
« on: 2013-07-01 10:13:23 » |
 |
All the work and effort of the NSA to get the ultimate computing power to crack encryption and now such flagrant flaunting and mocking of their incredible computing power by cell phone manufacturers, when the phones can be hacked with a pocket calculator it would seem. 
Cheers
Fritz
Tethered and vulnerable: Hotspot password FAIL not just in iPhones
Source: The Register
Author: John Leyden
Date: 2013.07.01
https://encrypted-tbn3.gstatic.com/images?q=tbn:ANd9GcS-P0rkR1PGyO53gu1Vzr7T5hlDbWVdywSsrsGpkDTLMkpzFMnFOw
Analysis The recent discovery that Apple's iOS hotspot passwords are readily crackable in under 50 seconds is part of a wider problem involving other smartphone platforms, claim researchers.
As recently reported by El Reg and others, a team of security researchers discovered from the University of Erlangen, Germany discovered that passphrases auto-generated by the "Personal Hotspot" are far weaker than Apple claims.
Bad though Apple's implementation is, other smartphone manufacturers support similar features and their approach is even worse in some cases, according to preliminary - and overlooked - findings from Andreas Kurtz, Felix Freiling and Daniel Metz, the three members of the Erlangen team.
Other mobile platforms might be affected by these deficits as well. Although we did not analyze other platforms in detail, spot-checks have revealed that default passwords in Windows Phone 8 consist of only 8-digit numbers. As this results in a search space of 108 candidates, attacks on Windows-based hotspot passwords might be practicable.
Moreover, while the official version of Android generates strong passwords, some vendors modified the Wi-Fi related components utilized in their devices and weakened the algorithm of generating default passwords. For instance, some Android-based models of the smart-phone and tablet manufacturer HTC are even shipped with constant default passwords consisting of a static string (1234567890).
However, future studies will be necessary to evaluate the security level of mobile hotspots on other platforms in more detail.
A more detailed look at the security shortcomings of hotspot implementation on other smartphones is not yet available. Kurtz told El Reg: "Unfortunately, we did not analyze other mobile platforms in detail."
The Erlangen team advises users never to accept the auto-generated passphrases suggested by mobile phones for Wi-Fi hotspots, even if the suggested password appears on casual inspection to be secure. The advice applies to all smartphones but derives from a close look at how Apple's technology works in practice.
Apple iPhones and iPads with 3G support can be used as Wi-Fi access points, a feature Apple calls "Personal Hotspot". The technology is designed with ease of use in mind, so Apple allows punters to generate a WPA passphrase that users can share amongst themselves and that can be typed in easily.
The password generator creates a pronounceable string of up to six characters, and combines it with a four digit number. That ought to give 30 billion possible combinations. A brute force attack using a decent laptop testing 3,000 WPA keys per second against a sniffed Wi-Fi session would take 120 days to run through all possible combinations.
This isn't a practical attack, but Kurtz, Freiling and Metz didn't take such assumptions for granted, instead deciding to investigate how the feature really worked.
Passphrase bingo
As a first step they generated a sample of Personal Hotspot passphrases. They wrote down the pronounceable word part of these login credentials before searching the internet to see if the words appeared together anywhere in a downloadable list. As it turned out these iOS Wi-Fi password words almost always seemed to appear as entries from a table used by an open source Scrabble game, containing a dictionary of 52,000 words.
If Apple was using words from this list in combination with a four digit number (which multiples the range of possible combinations by 10,000) then they were using a range of just 52 million possible passphrases.
At this point the researchers formed a tentative theory that the Apple passphrase generator has a dictionary list under the bonnet. To find out what going on the researchers set about disassembling the passphrase generator code.
They discovered that the software first fed a pseudo-random non-word into a spell checker and captured what came back before adding four pseudo-random digits. Only words of between four and six characters that happened to get returned by the spell checker were accepted.
The researchers wrote their own implementation of the passphrase generation code and ran it 100 million times with pseudorandom input. Only 1,842 different words came back, evidence that Apple's implementation was actually far worse than if the fruity firm had just used a Scrabble dictionary. Apple's tool generated only 18 million possible passphrases.
Encryption's fine - it's the passphrases that suck
Using a GPU rig of graphics cards, something many attackers would be able to access, the researchers discovered they needed just 50 seconds to run through all possible combinations - making it possible to brute-force crack a hotspot passphrase in less than a minute.
The researchers published their findings in a paper entitled, Usability vs. Security: The Everlasting Trade-Off in the Context of Apple iOS Mobile Hotspots. Kurtz, Freiling and Metz note that Apple's crypto-snafu is based on weak default passwords rather than a deeper problem with the WPA2 encryption protocol, which remains secure.
Paul Ducklin, writing on Sophos's Naked Security blog, said the issue means users need to come up with their own passphrase rather than accepting Apple's suggested login credentials.
"Anyone who knows your WPA key and is around when you connect to your network can decrypt your traffic in real time," Ducklin warns. "And anyone who is around when you connect and can sniff your traffic can attempt to crack the password and decrypt your traffic later. Choose your own passphrase, and make it a good one, when using iOS's Personal Hotspot," he concludes.
Kurtz, Freiling and Metz also advise avoiding default passwords in a summary of their research that explains why been able to crack passwords quickly is important to potential attackers.
"As it is always good advice to replace initial default passwords by user-defined strong and secure passwords, this becomes particularly relevant on mobile hotspots passwords," they conclude.
|




